Microsoft Windows SMB NULL Session Authentication
Introduction
nuclei - Ubuntu 22.04
nuclei
Burp Suite Certified Practitioner Certification
Burp Suite Certified Practitioner Certification
AutoRecon - Ubuntu 22.04
AutoRecon
Pentester Academy - PACES Certification - The Exam
I just completed my report for the PACES exam, and have submitted it to the support team. I’m not sure how long it will take before I get a response, or before I know if I have passed, but I am relatively optimistic that I have passed this exam.
How to pass your OSED exam
How to pass your OSED (Offensive Security Exploit Development) certification exam.
Dell Wyse 5010 Thin Client - Privilege Escalation
I recently had to perform a penetration test for a company that wanted to make sure the software being used for marking exams was secure. The software was running off the Dell Wyse 5010 thin clients, accessing a web application hosted on a Windows server.
Penetration Testing - Active Directory Labs
Resources for building your own Active Directory labs to “attack”.
SQLite Encryption - Data leak
During a recent engagement, we had to do a black box assessment of a software package that is used to monitor candidates while they take exams. The software provides a sandbox environment, and at the same time monitors various processes and actions performed on the computer at the time of taking the exam.
Powershell - Transfer Files
While busy with the PACES lab, I had to figure out a way to upload files to my attack machine. I couldn’t use tools like Netcat (nc.exe), because Windows Defender now picks this up as a malicious program.
Pentester Academy - PACES Certification
After a busy year (2020) of doing the Offensive Security courses, I decided to see what I can take next that would further my penetration testing skillset. Most of what I found was in line with what I’ve already done until I came across the PACES certification from Pentester Academy.
Powershell - Pivoting
I thought I’d share what I just stumbled upon while working on the PACES lab. I’m not really a Windows user, but while doing this lab you are forced in some situation to make use of and learn more about tooling that is available to penetration testers. What I found might not be news to anyone else, but once it worked I thought it was pretty cool.
TryHackMe - Plotted-EMR
It doesn’t feel like it’s often enough that hard rated rooms are released on Tryhackme, so when I see a new one pop up, I’m happy to take a stab at it.
Red Teaming - Building your dropbox
Introduction
Red Teaming - My first physical assessment
I’ve recently been given the opportunity to perform my first physical assessment during a black box engagement for a client.
SQL Injection - ORDER BY (Blind)
The story
OSCE3 - Started from the bottom.... now I'm here
Read MoreTryHackMe - Fortress
RaidForums - First Web Hacking Contest
I happened to come across this post on RaidForums, and decided to give it a go.
TryHackMe - Enterprise
My OSWE journey
As of 2021-08-07, I am officialy OSWE (Offensive Security Web Exploitation) certified. I must be lucky when it comes to Offensive Security exams, because I received my notification of a pass less than 24 hours after submitting my exam report.
TryHackMe - Crocc Crew
TryHackMe - Uranium CTF
Linode - Installing Kali Linux
It’s often needed for me to spin up a Linux box at a VPS provider, to help speed up recon during an engagement. It also helps testing infrastructure and web application from different IP addresses without having to switch between VPN connections.
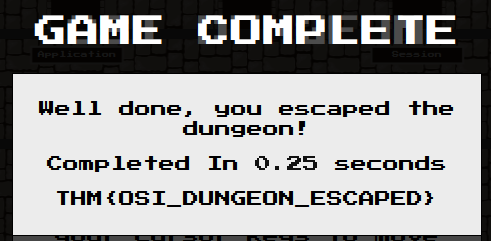
TryHackMe - OSI Model
Proving Grounds - Gaara
Gaara is a Linux box that is available on Offensive Security’s Proving Grounds. It’s rated as an Easy box.
Proving Grounds - Solstice
Solstice is a Linux box that is available on Offensive Security’s Proving Grounds. It’s rated as an Easy box, and rightfully so. There were a few rabbit holes, but if you considered all the variables before going down the rabbit hole, you would successfully avoid them.
My OSEP journey
As of 2021-06-16, I am officialy OSEP (Offensive Security Experienced Penetration Tester) certified. The email came as a bit of a surprise, especially since it arrived about 26 hours after I submitted my exam report.
The purpose of this site
I have been wanting to set up something that I can document my research, CTF, certification and work experiences for some time now. I finally decided to get this setup today.

